The European Union’s GDPR norms require IT security teams of businesses operating in the EEA to safeguard user identities. Hefty fines to the tune of 20 billion euros and irrevocable reputational losses have spurred massive investments in data protection services. Particularly, the global spending on identity and access management (IAM) solutions is expected to exceed $16 billion USD by 2022. It is, therefore, the legal responsibility of global businesses to implement effective IAM strategies to comply with GDPR regulations.
This blog post discusses the significance of IAM and its core practices in establishing GDPR compliant digital businesses.
Identity and Access Management or IAM is a business security protocol that ensures regulated access of user information to authorized individuals. It ensures that only the right individuals have access to critical business data including employee and customer identities.
Articles 5, 24, and 32 of the GDPR necessitate businesses to have an IAM system in place. They mandate businesses to monitor the processing of personal data, implement threat prevention measures, and restrict access to sensitive data.
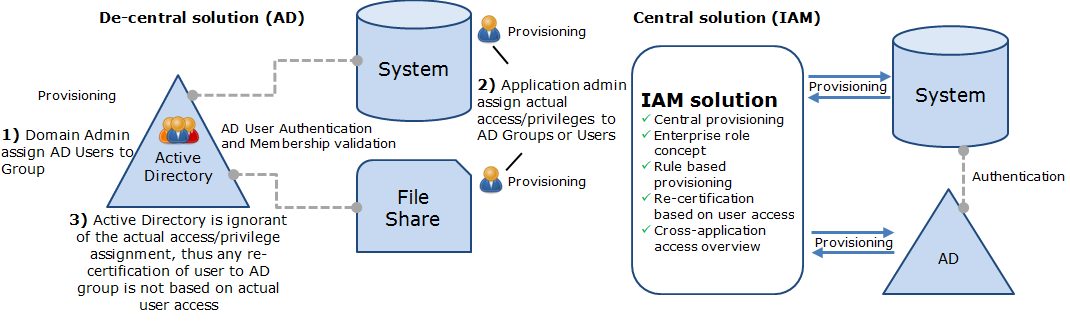
Traditionally, businesses used a manual access control process such as Active Directory that involved grouping of members to access confidential information. However, the cumbersome method was ineffective at managing individual access to resources. It clearly violated GDPR guidelines and obliged businesses to seek end-to-end data protection solutions such as IAM.
Within an organization, information mismanagement and leakage due to multitasking among several software programs. An employee’s typical working day involves multiple log-ins into email accounts, dashboards, backend systems, and other applications with distinct credentials. The need to remember and secure usernames and passwords for gaining access to all essential systems can be challenging.
To combat the above-mentioned challenges, organizations adopt SSO systems that support the following characteristics-
a) SSO or Single sign-on is a core IAM requirement for businesses to ensure GDPR compliance.
b) It enables an authenticated employee access to business resources and assets with a centralized gateway entry for all.
c) Organizations can run SSO software on-premises, use a cloud-based service or take a hybrid approach to prepare an SSO-friendly architecture.
2FA or multi-factor authentication is another proven methodology used by privacy and data protection services teams. It involves OTP-backed log-ins, mobile synchronization, and AI-powered captcha gateways to ensure authenticated user access.
Businesses must adopt a federated authentication process to govern the sharing and exchanging of organizational data with partners and clients. It ensures secure and controlled business interactions without compromising sensitive information as per GDPR guidelines.
Segregation of duties (SoD) is a fraud prevention methodology that mandates two or more employees to break an access point. Doing so, businesses can mitigate the risk of single dominant access by increasing the number of stakeholders for a single task.
SoD requires a well-planned and decentralized security infrastructure. Over the years, several industry giants, financial institutions, and eCommerce businesses have implemented SoD in their IT systems to ensure GDPR compliance.
In 2016, Deutsche Bank implemented a centralized IAM system and an API architecture to enable role-based access to business systems. The method eliminates segregation of duties violations and carries out access rights management and regular review. Also, the system automatically revokes access rights when employees change roles or leave the bank.
Related- GDPR Compliance | Best Practices for Mobile App Data
In a bid to promote digital transformation, it is essential for customer-oriented businesses to support robust data protection and security solutions.
At Oodles, we provide multidimensional data privacy and protection services to global businesses. We implement the privacy by design concept, to ensure privacy protection is embedded in business processes, physical design, networked infrastructure, information technology, etc. Talk to our data analysts to know more about our work and services.